In my previous post “What is your excuse for passwords”, I wrote about going passwordless all the way and how to enroll a Windows device with Autopilot using Azure Temporary Access Pass (TAP), and a FIDO2 security key. Working passwordless on Windows is easy, but when it comes to working passwordless on Mobile devices like Android and iOS, there are some other considerations. That being said, It is possible and in this post, I’ll show you that mobile devices are not an excuse for passwords.
You can very well be working passwordless on mobile devices (corporate and personal). We’ll have a look at phone sign-in with the Microsoft Authenticator app and also enroll for a work profile with the Company Portal app and sign-in from another device using a FIDO2 security key.
This post will focus on enrolling Android devices and configuring applications like Outlook and Teams, without a password. I’ll follow up with another post for iOS devices, but in general, the procedures are the same. Although, you don’t have a work-profile option for iOS. If you want to skip to the user experience video, have a look at my YouTube Channel
Passwordless sign-in to outlook on Android devices
Imaging you have a user that is enabled for passwordless, and this user want’s to configure Microsoft Outlook on a personal Android device. My test user for this demo is Jessy Wonka. She also completed the passwordless enrollment of a Windows device in my previous post.
Currently you can’t use a FIDO2 security key to sign-in to Outlook for mobiles. Then what options are there to support this scenario? The answer is passwordless sign-in with the Microsoft Authenticator app. The Authenticator app can be used to sign in to your Azure AD account without using a password on any device platform, including mobile devices like Android and iOS. And on iOS you can now use multiple accounts (in preview right now)! Microsoft is also working on multiple account support for Android and I hope this will become available anytime soon.
Passwordless sign-in with the Microsoft Authenticator app
Please read the official documentation on passwordless sign-in with the Microsoft Authenticator app to learn more about the prerequisites and how to enable this in your tenant. Also read Use Microsoft managed settings for the Authentication Methods Policy to learn more about the configuration options.
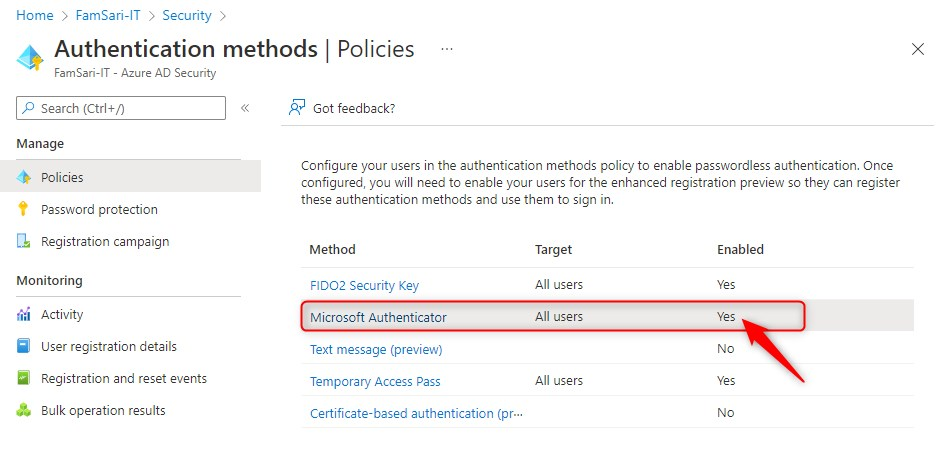
To enable the Microsoft Authenticator app for passwordless sign-in go to Azure Active Directory > Security > Authentication methods > Policies. Click on Microsoft Authenticator and then enable the policy for all your users.
Now that we have enabled the Microsoft Authenticator app for passwordless sign-in, let’s have a look at some of the Android device scenario’s we have;
- Personal Android device
- Scenario 1: Without App protection policy
- Scenario 2: With App Protection policy
- Scenario 3: Personal owned with work profile
- Corporate Android device
- Scenario 1: Corporate-owned dedicated devices
- Scenario 2: Corporate-owned, fully managed user devices
- Scenario 3: Corporate-owned devices with work profile
Working Passwordless on personal Android devices
For this demo, I’m going to assume you have configured an app protection policy to protect corporate data on personal devices. So I’m going to skip to scenario 2: With App Protection Policy.
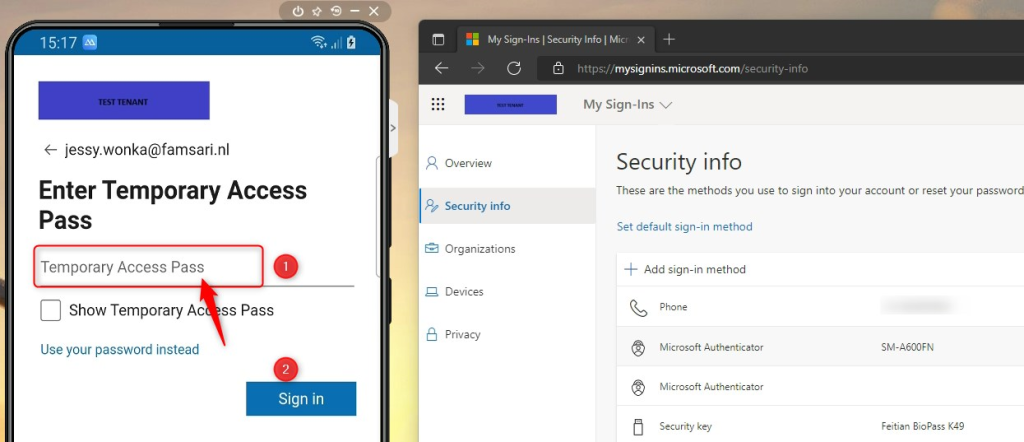
Before you continue, make sure to assign a Temporary Access Pass (TAP) to the test account you use! You’re going to use this TAP to add an account to the Microsoft Authenticator App. Watch the video on my YouTube channel to learn more about TAP. Now let’s start working passwordless on mobile devices shall we?
working passwordless on Personal Android devices – Scenario 2: With App Protection policy
Since it’s a personal device first install the Microsoft Outlook app from the store. Then go ahead and also install the Microsoft Intune Company Portal app (for App protection policy support) and the Microsoft Authenticator app (for passwordless sign-in).
Make sure you communicate a work-flow for your end-users. This will help them follow the right steps during enrollment and configuration. The workflow below is what I use. Your scenario might require another work-flow.
- Start the Authenticator app and add a work or school account like you always do
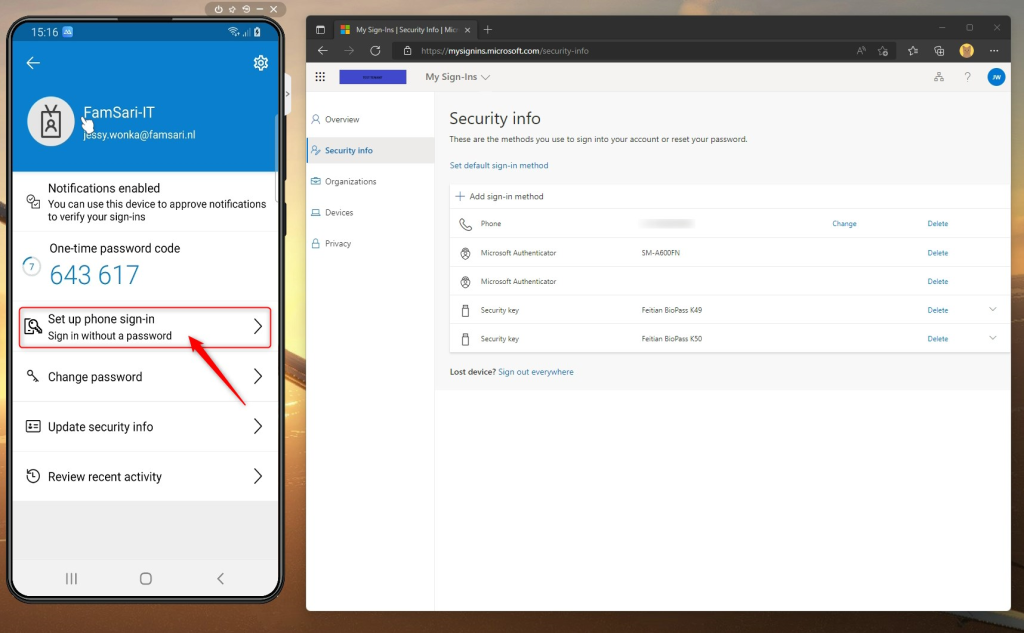
- Jessy Wonka can sign-in to https://aka.ms/mysecurityinfo on any Windows device using a browser and the FIDO2 security key she already has configured. (read my previous post for more info)
- After adding a work or school account. Click on the account in the Authenticator app
- Click on Set up phone sign-in
- Follow the steps
- Enter your Temporary Access Pass when asked to.
- Click on Sign in
- Then follow along to register your Android device.
- When you are done registering the device, you are ready for working passwordless on mobile devices.
Passwordless sign-in to Outlook app
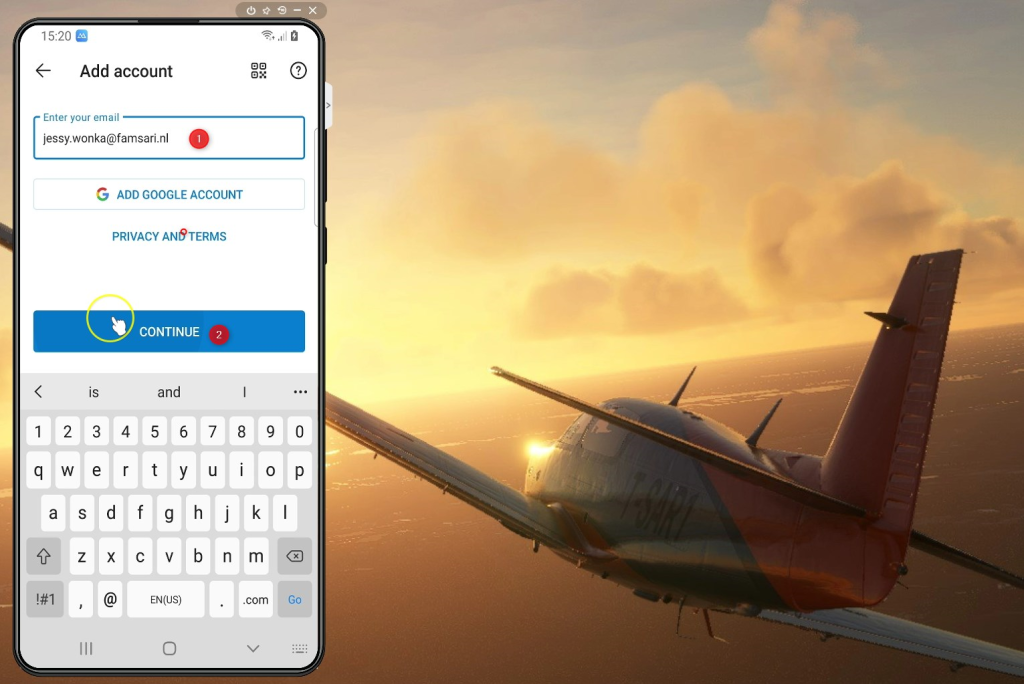
Let’s continue and add an account to the Outlook app. First open the Microsoft Outlook app on your Android device. It should detect your account, but if it doesn’t you’ll have to enter your e-mail address to continue.
- Enter your email address
- Click on Continue
Now things start to get interesting.
- Click on Send notification
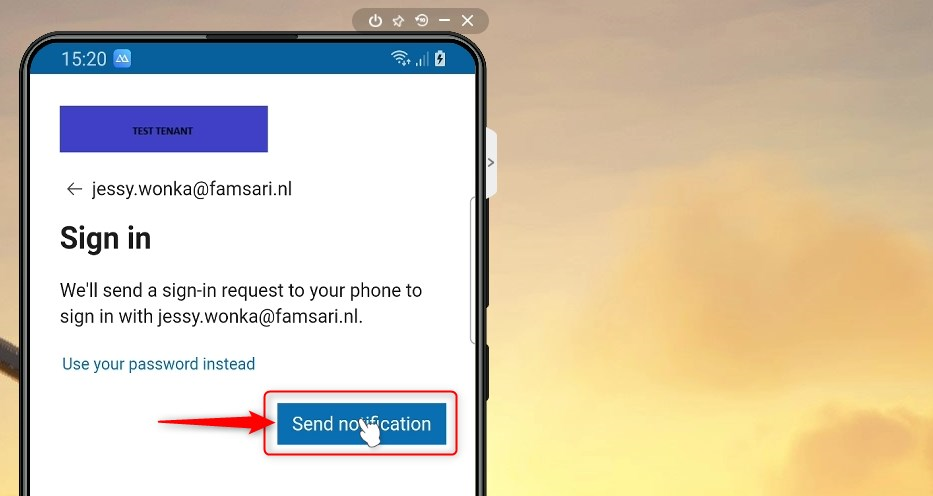
- When you click on Send notification, you will see a number appearing in your screen.
- You’ll also see a sign-in request notification.
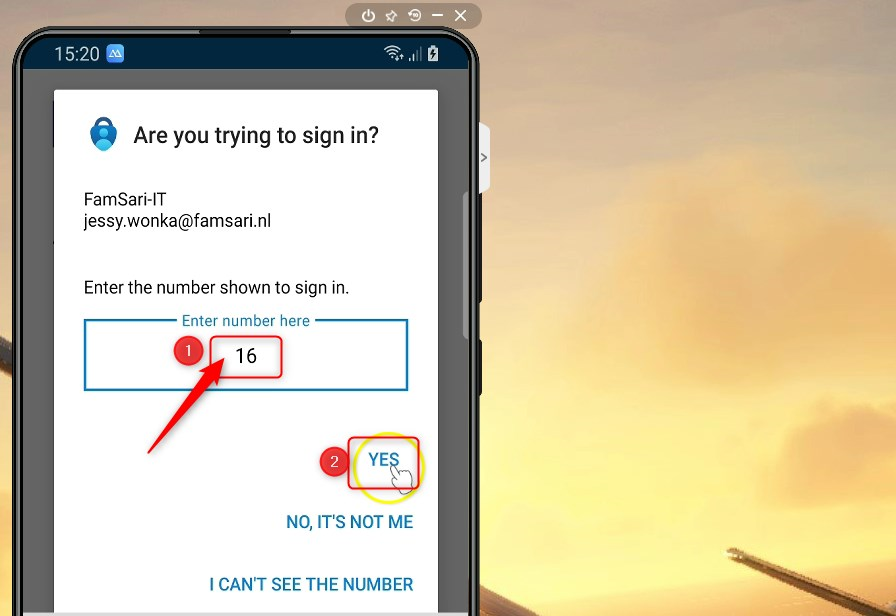
- Click on the sign-in notification
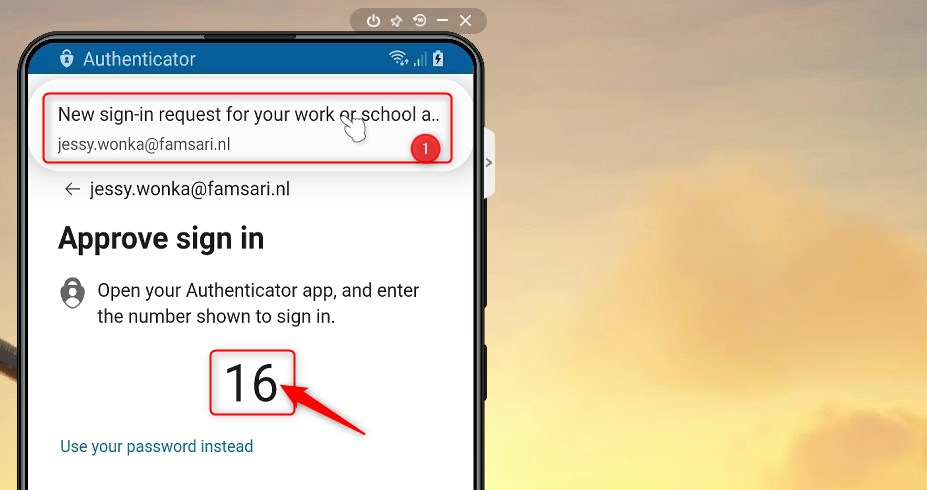
- Enter the number you’ve seen and click on YES
Since I have configured App protection policies in my test tenant, I’ll have to click through some other screens, and then a little later on, I’ll sign-in to Outlook on my Android device. And all this, without the need for a password. You see? Working passwordless on mobile devices is not that hard!

Working passwordless on Personal Android devices – Scenario 3: Personal Owned with Work profile
Let’s have a look another scenario. The personal owned with work profile option enables you to fully separate the personal profile from the work profile by providing the option to switch between 2 profiles. All your work related stuff, works in its own container. There are organizations that only allow Android for Work Profile. If you have this requirement, you might want to read my other post on Blocking access to Microsoft 365 outside the Android for Work Profile with Endpoint Manager
To enroll a Personal Android device for a work profile, open the Company Portal app and sign in with your work account.
You can again use a TAP, but I also want to show you another option to sign-in to the company portal app. Namely, the option to “sign in from another device”. This option is ideal for users who work passwordless and have configured a FIDO2 Security key. My test user Jessy Wonka has already configured a security key, so we’ll use a security key instead of a TAP to sign in from another device.
- Install the Company Portal app from the store
- Start the Company Portal app
- Instead of using a username and password, click on Sign-in options
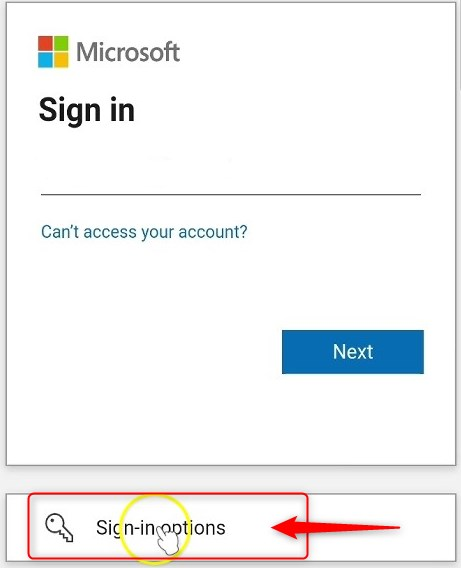
Company Portal App sign in from another device
- Click on “sign in from another device”.
- On a Windows device go to https://microsoft.com/devicelogin
- Enter the code from your mobile phone in the browser
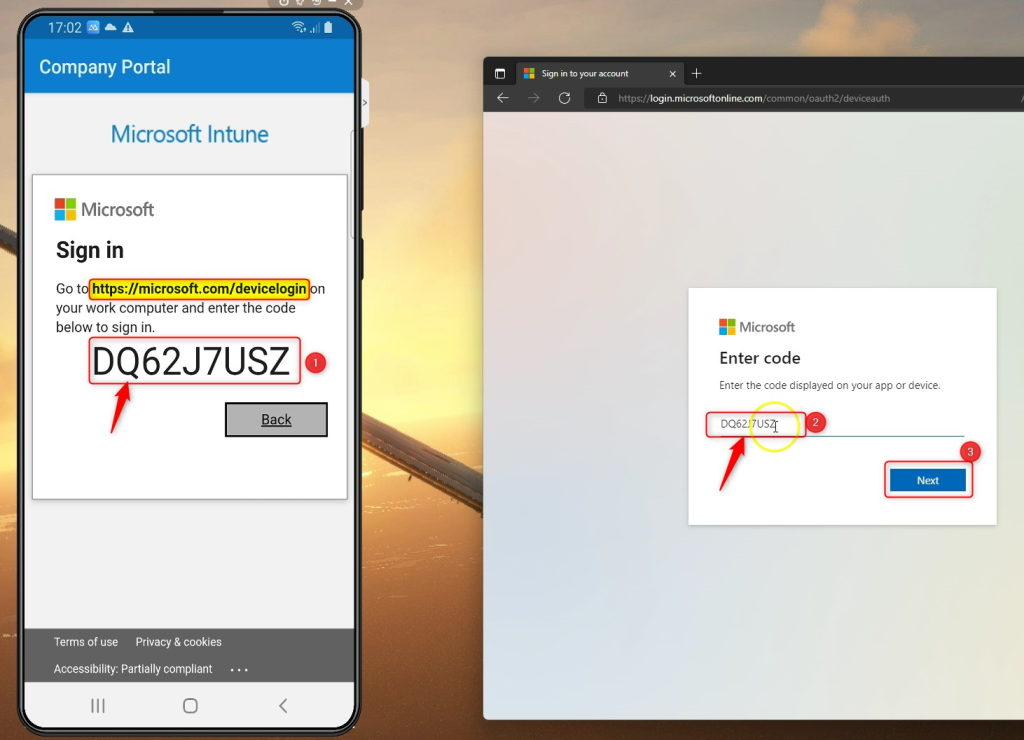
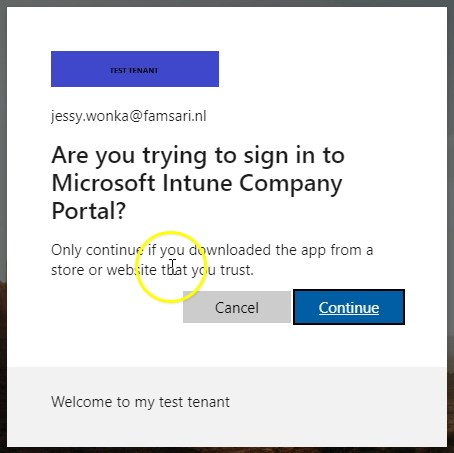
- Sign in using the test account you’ve configured. In my case it’s Jessy Wonka.
- Use the FIDO2 Security key for passwordless sign-in
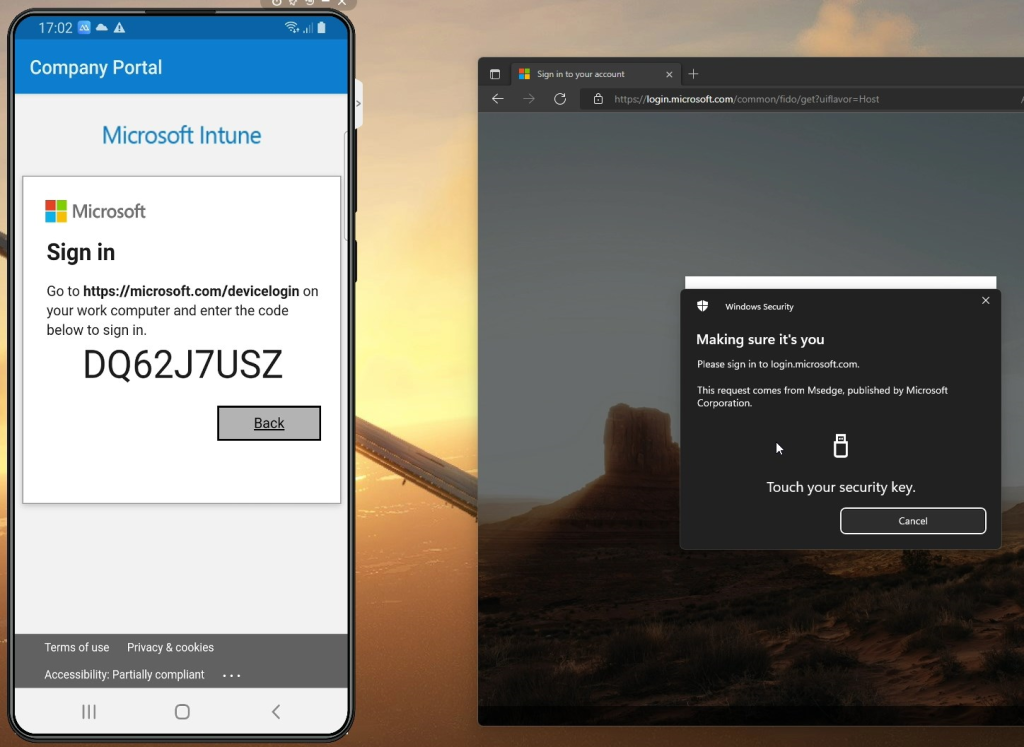
- When you sign-in successfully, Click on continue to complete the sign-in on your mobile phone.
- You can now close the browser on your Windows device and continue on your mobile device.
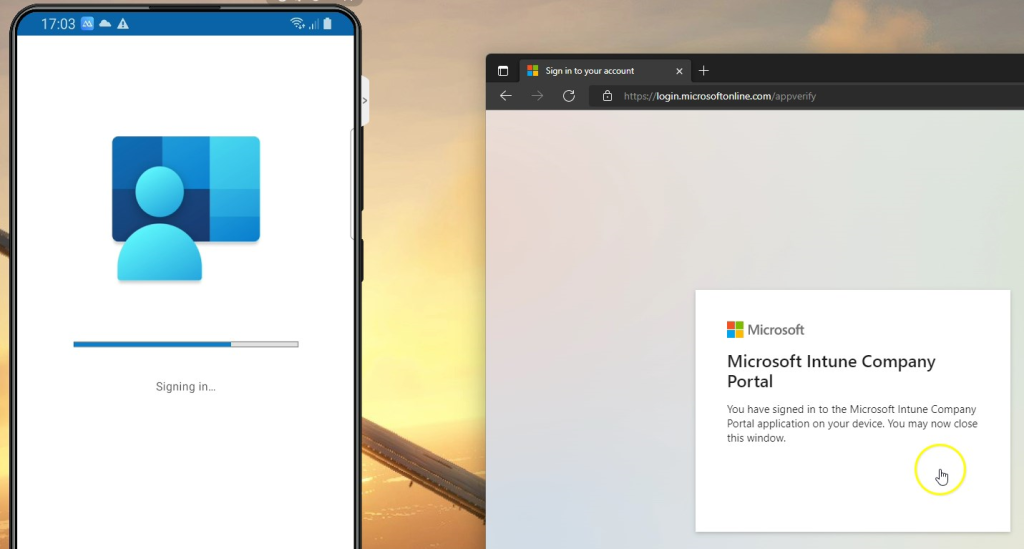
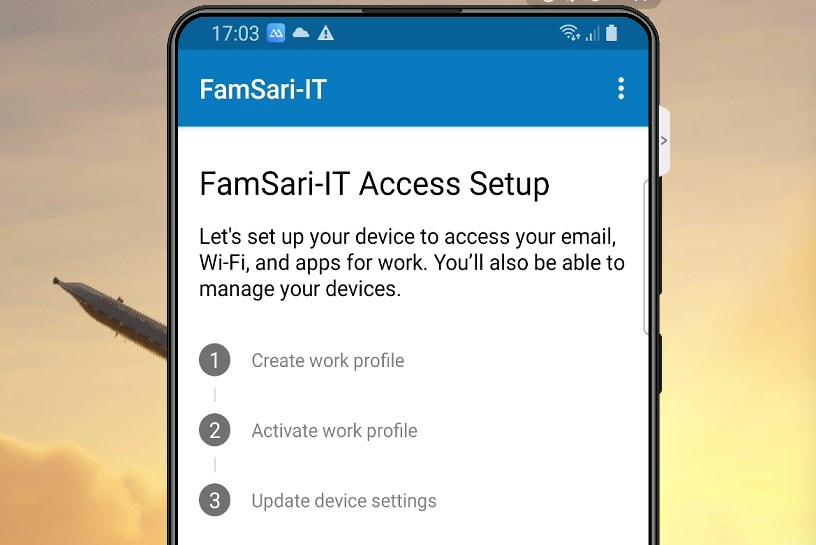
The Company Portal app will help you continue with creating a work profile.
- Follow the steps to complete.
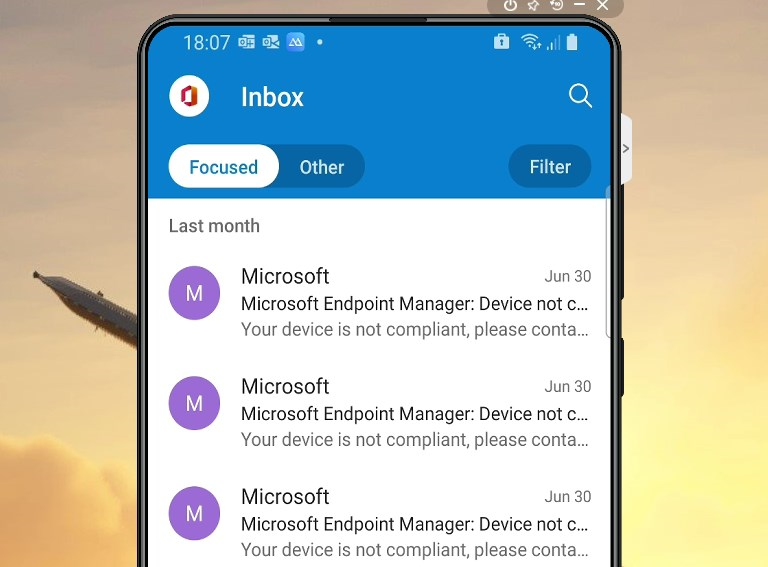
When you are ready with your work profile, wait for the work apps to install. When all apps have been installed, you can start Outlook for example. The sign-in user experience is vey smooth from here on.
And once again, we’ve completed a passwordless enrollment and configuration of Outlook on a Android device, without ever knowing the actual account password. Working passwordless on mobile devices now looks easy enough right?
Working passwordless on Corporate owned mobile devices?
I might do a dedicated post on corporate owned devices, but in short, you will use a TAP to enroll the device. The “Sign in from other device” option will also work. When you do use TAP, make sure you set one-time-use to No, because you will need to use the TAP multiple times. For those interested, see the below “In a nutshell”:
Corporate-owned, fully managed user devices
- Scan QR to enroll device
- Sign in to Google chrome using TAP or “Sign in from other device”
- Register device
- Sign in to Intune app with TAP
- Register device
- Open company portal app
- Open outlook
Summary
Basically, when it comes down to working passwordless on mobile devices, you will be using a Temporary Access Pass for the enrollment process. You also use TAP to add a work account to the Authenticator App for passwordless sign-in. After that, you are ready to work on your mobile device.
Working passwordless on mobile devices – User experience
Here’s a short video showing you the user experience on a Android device in both the above scenario’s. Hope you’ll find this post interesting enough to give it a try. I encourage you to participate and leave your feedback or comments below. That is very much appreciated.

[…] https://allthingscloud.blog/working-passwordless-on-mobile-devices/ […]
[…] Working passwordless on Mobile devices. Working passwordless on mobile devices is easy. In this article author shows that mobile devices are not an excuse for passwords. […]
It worked for me. But with a personal phone and scenario 2 I did not need to setup the phone authentication. And for the intune app this feature does cost your employer every month so not all are willing to pay for this service.